Comprehensive Data Security Risk Assessment
Leverage globally recognized standards like BS7799, ISO 17799, and Information System Security Data Security Risk Assessment to evaluate your data security risks. Receive detailed reports and customized cybersecurity solutions to safeguard critical assets.

Why Risk Assessment Matters
Modern businesses face escalating cyber threats and regulatory demands. Proactive risk management, rooted in precise assessments, enables organizations to prioritize threats, allocate resources efficiently, and implement cost-effective safeguards aligned with legal and operational needs.
Key Service Advantages
Service Overview
NCDefence’s Data Security Risk Assessment combines cutting-edge tools, certified experts, and minimal operational disruption to deliver:
Holistic Evaluation: Network, host, application, database, and middleware analysis.
Advanced Threat Detection: Remote vulnerability scanning, configuration audits, and threat likelihood analysis.
Actionable Insights: Risk severity grading, mitigation strategies, and remediation plans tailored to your risk tolerance.
Framework Highlights
Technical & Management Audits: Identify security gaps in systems and policies.
Real-Time Risk Prioritization: Focus on high-impact vulnerabilities.
End-to-End Support: From assessment to reinforcement recommendations.
Holistic Evaluation: Network, host, application, database, and middleware analysis.
Advanced Threat Detection: Remote vulnerability scanning, configuration audits, and threat likelihood analysis.
Actionable Insights: Risk severity grading, mitigation strategies, and remediation plans tailored to your risk tolerance.
Framework Highlights
Technical & Management Audits: Identify security gaps in systems and policies.
Real-Time Risk Prioritization: Focus on high-impact vulnerabilities.
End-to-End Support: From assessment to reinforcement recommendations.
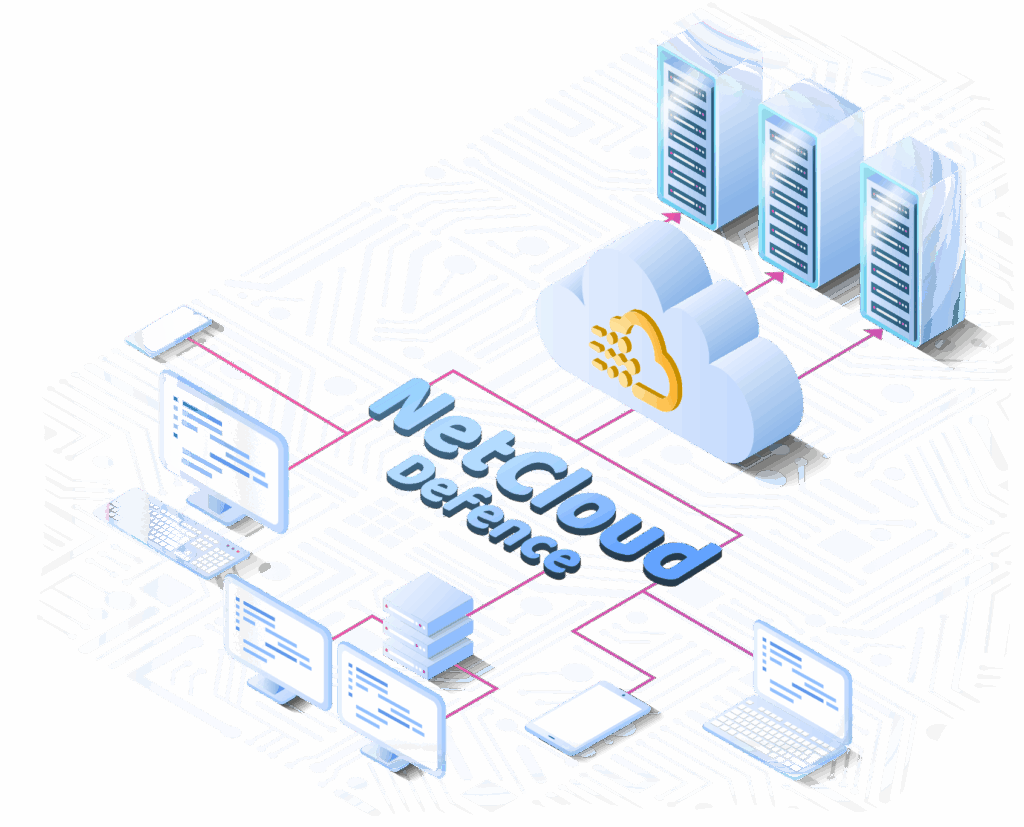
Data Security Risk Assessment – Program Architecture

Scope of Data Security
Risk Assessment

Network Security Assessment

Host Security Assessment

Application Security Assessment

Database
Assessment

Middleware
Assessment

Security Management Assessment

Methods for Data Security
Risk Assessment

Security
Scanning

Security
Auditing

Manual
Scanning

Security Policy Assessment

Phases of Data Security
Risk Assessment

Assessment
Design

Security Assessment Implementation

Security Management Assessment

Measures and Recommendations
Strategic Vendor & Partner
Our Certification

ISO / IEC 27001
ISMS
ISMS

Cybersecurity Review
of China
of China

Information Technology Service Standards (ITSS)

Registration of 31 Computer Software Copyrights

China Cybersecurity Review Technology and Certification Center
Contact Us
You’re not a customer yet and would like to discuss our services?
Join Our Global
Cybersecurity Alliance
Whether you’re an enterprise seeking protection or a tech provider expanding capabilities, let’s build safer digital ecosystems.